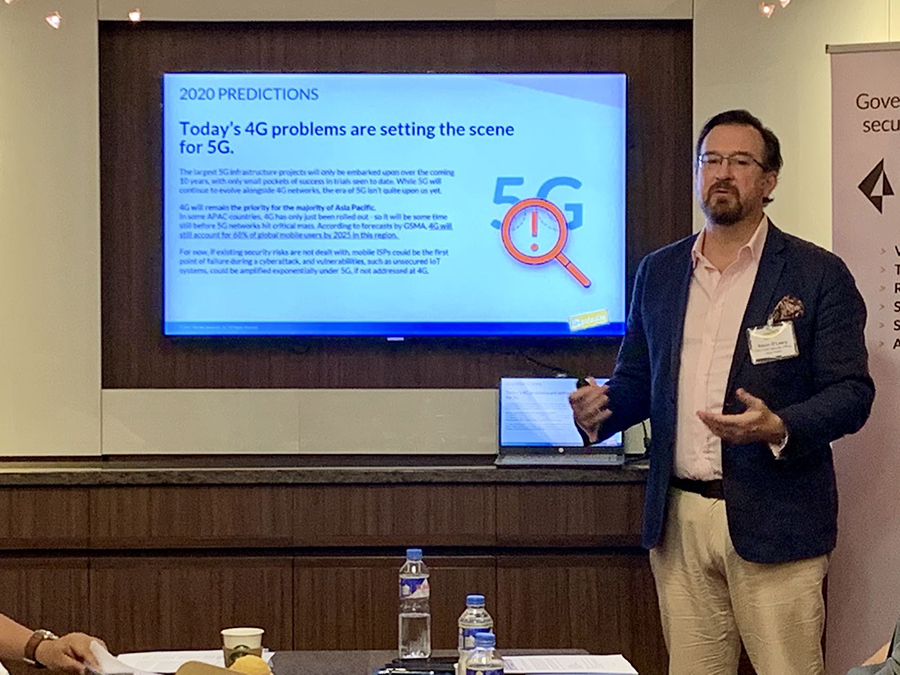
Prediction: 4G will remain the priority for the majority of Asia Pacific
The largest 5G infrastructure projects will be embarked upon over the coming 10 years, with only small pockets of success in trials seen to date. While 5G will continue to evolve alongside 4G networks, the era of 5G isn’t quite upon us yet. In some APAC countries, 4G has only just been rolled out, so it will be some time still before 5G networks hit critical mass. According to forecasts by GSMA, 4G will still account for 68% of global mobile users by 2025 in this region. Many rural areas could still operate under LTE models, simply due to the longer range of 4G, compared to 5G’s mmWave.
If existing security risks are not dealt with and roll over, mobile ISPs could be the first point of failure during a cyberattack, and vulnerabilities, such as unsecured IoT systems, could be amplified exponentially under 5G if not addressed at 4G. New cybersecurity approaches are needed today, including adopting a preventive approach to security, increasing levels of security automation, establishing contextual security outcomes and integrating security functions with APIs. We foresee that 4G will continue to be targeted by hackers as a potential gateway to 5G networks over the next few years.
The talent shortage isn’t what you think it is.
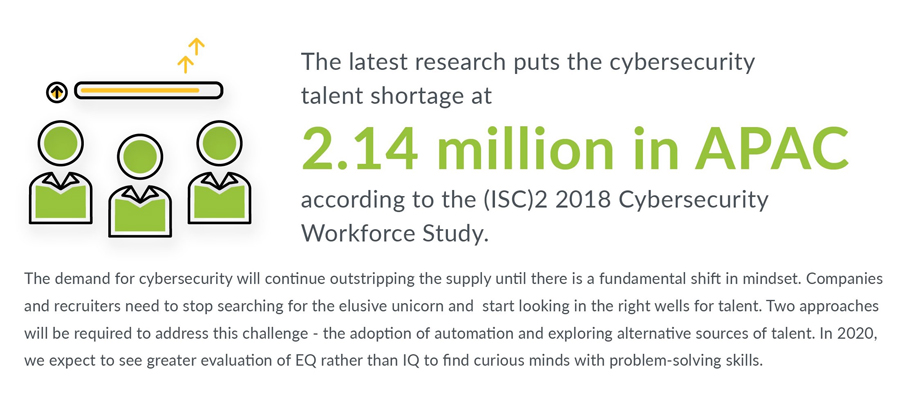
Prediction: Curious minds and problem solvers wanted
The demand for cybersecurity will continue outstripping the supply until there is a fundamental shift in mindset. Two complementary approaches will be required to address this challenge: the adoption of automation and exploring alternative sources of talent.
Automation is going to be a key element in the future of cybersecurity because human operators should not be required – and expected – to do everything. Instead, they need to harness skill sets that cannot be automated and focus on higher-order tasks, such as problem-solving, communication and collaboration. This will necessitate a reexamination of today’s security operating centre (SOC) structure, and a corresponding change in the types of professionals needed for these new roles, in order to accurately identify and fill some of these gaps. Companies and recruiters need to stop searching for unicorns (they don’t exist!) and start looking in the right wells for talent.
In 2020, we expect to see greater evaluation of EQ rather than IQ to find curious minds with problem-solving skills, be they engineers, analysts or even communications specialists. Investments need to be made to upskill and cross-skill these overlooked sources and groom these capable individuals into the talent we need. The workforce category in the NICE Framework is a helpful and practical starting point for companies looking to accurately identify the relevant cybersecurity skills gaps within an organisation.
Navigating IoT will become a minefield for everyone.

Prediction: Your wireless doorbell might welcome more than your visitors
In 2020, we will see the evolution of IoT security play out in two key spheres: Personal and Industrial IoT. From connected doorbell cameras to wireless speaker systems, we will see a growth in attack modes coming in via unsecured apps or weak login credentials. This threat is further complicated by the emergence of accessible deepfake technology, which can pose a threat for voice- or biometric-controlled connected devices. The mimicry of what were once the strongest biological identifiers to access and control connected systems will have an impact beyond the homes of individuals and into the enterprise environment.
For enterprises, one sector in which we expect to see significant changes take effect is manufacturing, a key pillar of many Asian economies. Manufacturers are looking to deploy sensors, wearables and automated systems as a way to streamline production, logistics and employee management via data collection and analytics. Organisations will need to ensure that these connected devices can leverage automated features, such as built-in diagnostics, continuous vulnerability scanning and advanced analytics in order to remain on top of threats.
Connected devices will need to be continuously retrofitted and updated in order to remain secure. There also is a growing trend among governments globally – including those in Asia Pacific- to issue guidance or regulations related to IoT device security. Further, efforts also are ongoing in industry standards groups to develop relevant security standards for IoT devices, such as the draft ISO/IEC 27037 standard. Both of these trends are certain to impact IoT device deployment to some degree. We also expect prioritisation of public education to accompany the rapid growth and adoption of connected devices.
The data privacy lines get blurrier.
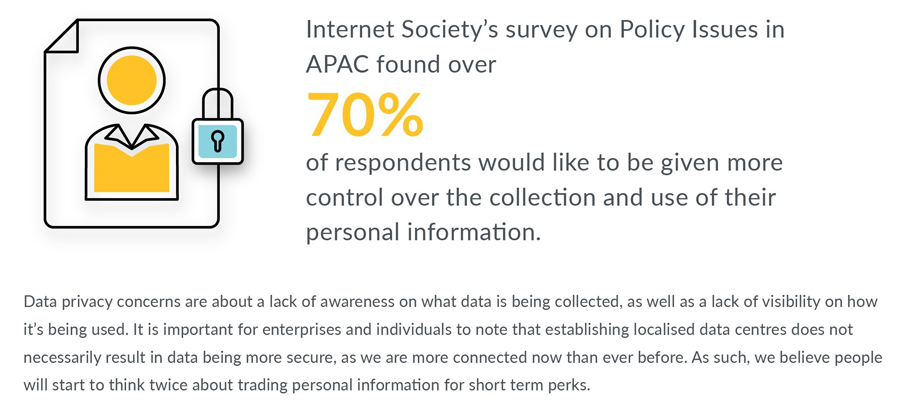
Prediction: More data privacy legislation, and the data sovereignty-security paradox
We expect additional data privacy legislation to emerge in the region. Both Indonesia and India have been working on personal data protection bills for the last few years, although the timing for if and when these become final is unclear. A growing number of proposals in the region also would require housing data in its country of origin; these tend to be driven by privacy and security concerns. The latest draft of Indonesia’s Government Regulation No. 71 of 2019 would mandate that public agencies must manage, process and store data within Indonesia (according to unofficial translations). We expect more regulatory proposals that regulate or restrict the movement of data across borders, particularly public sector information. In response, it is likely that companies may look to build more data centres locally to support in-market customers better.
However, it is important to note that establishing localised data centres does not necessarily result in data being more secure. Individual end users or corporations are increasingly connected and vulnerable to global incidents, as cyberthreats do not respect national borders. Businesses are still responsible for adopting a comprehensive cybersecurity strategy that supports operations and information held across the network, endpoints and the cloud. To manage this effectively, companies will need to regularly evaluate the value of the information they collect and control its access.
We foresee that enterprises will need to pay even closer attention to their data flows in a highly interconnected region like ASEAN. Despite efforts to create a regionally harmonized approach to personal data protection—such as via the voluntary APEC Cross-Border Privacy Rules—there is no true harmonization. To create a framework that best serves the region, close collaboration between the private and public sectors will be needed to evaluate how breaches are identified and defined in the face of continuously emerging threats.
The cloud future has arrived: Don’t get lost in turbulence.

Prediction: More confusion on configuration
More businesses are leveraging containers (i.e., operating system virtualisation) for their efficiency, consistency and lower costs. However, the potential dangers of exposed and misconfigured containers will soon rear their ugly heads, leaving organisations vulnerable to targeted reconnaissance. Using the proper network policies or firewalls, or both, can prevent internal resources from being exposed to the public internet. Additionally, investing in cloud security tools can alert organisations to risks within their current cloud infrastructure.
Cloud security adoption has its own set of challenges as well. Commissioned by Palo Alto Networks, Ovum’s Asia-Pacific Cloud Security Study has found that 80% of large organisations view security and privacy as key challenges to cloud adoption.
Key findings include:
⦁ 70% of large organisations in APAC have misplaced confidence in cloud security, believing security by cloud providers alone is sufficient.
⦁ Large organisations in APAC have many security tools, which creates a fragmented security posture and adds further complexity to managing security in the cloud, especially if the companies are operating in a multi-cloud environment.
⦁ There is need for automation, given that large organisations do not have enough time and resources to dedicate to cloud security audits and training.

2020 will also see more companies move towards a DevSecOps approach, integrating both security process and tools into the development lifecycle of new products. This will be the way forward for integrating cloud and containers successfully.
If existing security risks are not dealt with and roll over, mobile ISPs could be the first point of failure during a cyberattack, and vulnerabilities, such as unsecured IoT systems, could be amplified exponentially under 5G if not addressed at 4G. New cybersecurity approaches are needed today, including adopting a preventive approach to security, increasing levels of security automation, establishing contextual security outcomes and integrating security functions with APIs. We foresee that 4G will continue to be targeted by hackers as a potential gateway to 5G networks over the next few years.
Liked this post? Follow SwirlingOverCoffee on Facebook, YouTube, and Instagram.

