Last year, Kaspersky experts witnessed a significant uptick in stealers and extortion activities on the dark web market. Looking ahead, the company also anticipates new challenges, including a heightened presence of crypto-drainer services, increased promotion of fraudulent websites through search advertising, and a rise in malicious “loaders”.
In the latest Kaspersky Security Bulletin (KSB), experts from Global Research and Analysis Team and Kaspersky Digital Footprint Intelligence have compiled a comprehensive review of the past year and provided insights into emerging trends in the shadowy dark web market – a central hub for illicit services within the cybercriminal community.
2023 Highlights:
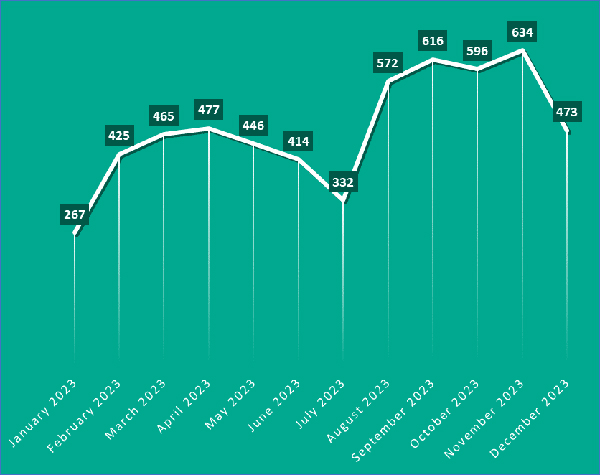
- Ransomware blog posts saw a surge
Ransomware actors typically create blogs for blackmailing companies, revealing new successful hacks of businesses or as a place to post stolen data. In 2022, there were around 386 monthly blog posts on public platforms and the dark web. In 2023, the average surged to 476, peaking in November (634 posts).
- Personal and corporate credentials faced an escalating risk of leakage
The dark web market saw a rise in posts related to stealer malware, designed to pilfer sensitive information such as login credentials, financial details, and personal data. Cybercriminals sell this data to other malicious actors for identity theft, financial fraud, or other illicit activities.
Notably, posts offering Redline stealer logs, a popular malware family, tripled from an average of 370 per month in 2022 to 1,200 in 2023. Overall, the volume of various malware malicious log files, containing compromised user data and freely posted on the dark web, rose by almost 30 percent in 2023, compared to the previous year.
As Kaspersky looks ahead to 2024, several trends are expected to shape the landscape of dark web market:
- Scammers will increasingly turn to search engine advertising to promote websites embedded with malware
Previously reliant on phishing emails, cybercriminals now employ Google and Bing ads to ensure their landing pages – embedded with malware – receive top positions in search results. Black traffic dealers are likely to escalate their sales activities in the underground market, and Kaspersky expects a continued rise in these deceptive practices.
- Growing demand for crypto-drainer services
Crypto drainers, a category of malicious software engineered for the swift and automated withdrawal of funds from legitimate crypto wallets to malicious actors’ wallets, are gaining momentum among crypto scammers. Kaspersky forecasts a rise in demand for this kind of crypto-stealing malware, resulting in an increased prevalence of advertisements promoting its development and sale in the underground market. The sustained interest in cryptocurrencies, NFTs, and related digital assets is expected to fuel the proliferation of these drainers.
Apart from that, experts anticipate the following tendencies:
- The number of services providing AV evasion for malware (crypt) will increase
- “Loader” malware services will continue to evolve
- Bitcoin mixers and cleaning services will continue to evolve and exhibit dynamic market changes
“Cybersecurity demands a proactive stance. Monitoring dark web market activities and trends is akin to peering into the enemy’s playbook, allowing early threat detection, understanding adversary tactics, and ensures you’re several steps ahead in terms of cyber defenses. It’s not just about protection; it’s about mastering the evolving threat landscape to fortify against tomorrow’s risks and ensure the resilience of corporate security,” says Sergey Lozhkin, Principal Security Researcher, Global Research and Analysis Team (GReAT) at Kaspersky.
The dark web market predictions and review are part of Kaspersky Security Bulletin (KSB) – an annual series of predictions and analytical reports on key shifts within the cybersecurity world. Follow this link (https://securelist.com/darknet-predictions-for-2024/111763/) to learn more.
Liked this post? Follow SwirlingOverCoffee on Facebook, YouTube, and Instagram.